Introduction: Why Enterprise Data Breaches Are Escalating in 2026
Enterprise data breaches are no longer isolated cybersecurity incidents, they are now continuous, high-impact business risks affecting global organizations. In fact, the average cost of a data breach has reached $4.45 million, with enterprise-level incidents often exceeding this significantly depending on industry and scale.
As enterprises expand across cloud environments, SaaS platforms, and remote infrastructures, their attack surface continues to grow exponentially. As a result, security complexity is now one of the biggest operational challenges for modern organizations.
Moreover, cybercriminals are evolving faster than traditional defense systems. Instead of relying on manual attacks, they now use AI-driven phishing, automated credential theft, and advanced social engineering techniques. Consequently, even highly mature enterprises are falling victim to preventable failures.
In addition, most breaches today do not originate from unknown threats, they originate from known, repeated security gaps such as weak access control, delayed patching, and poor monitoring.
Key insight: Over 80% of enterprise breaches involve human error or misconfiguration, not advanced hacking techniques.
Therefore, understanding these mistakes is critical for building a resilient cybersecurity strategy. This blog breaks down the 5 most costly mistakes that lead to enterprise data breaches, and How Cyberix helps organizations eliminate these risks before damage occurs.
What Is an Enterprise Data Breach?
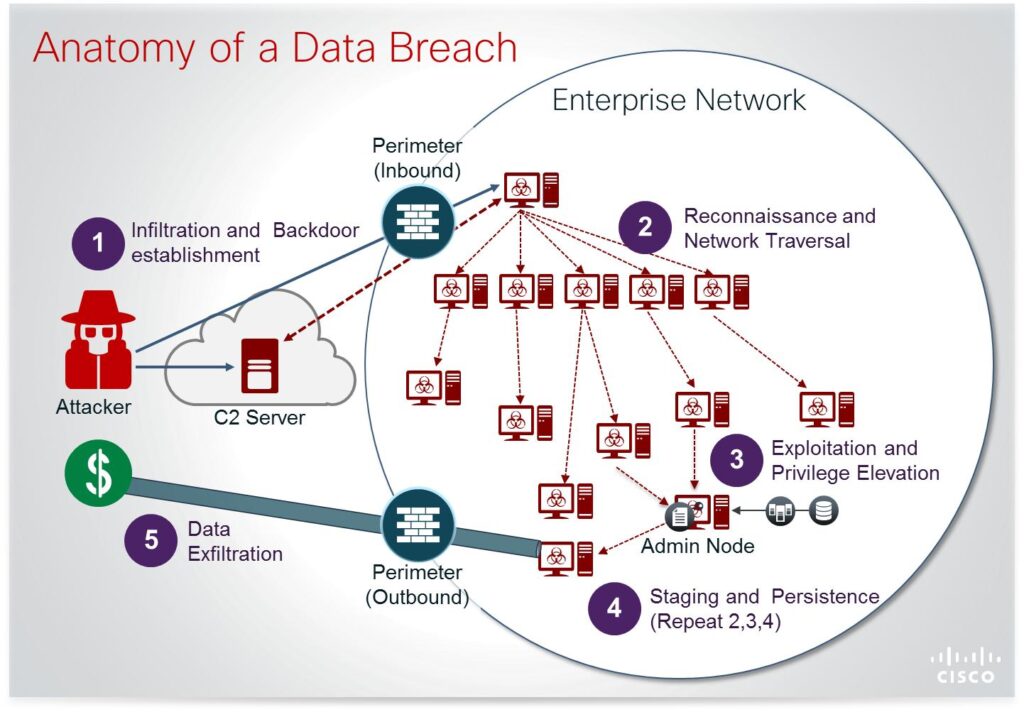
An enterprise data breach is a cybersecurity incident where unauthorized individuals gain access to sensitive business data such as customer records, financial systems, intellectual property, or internal operations. These breaches typically occur due to weak security controls, misconfigurations, or system vulnerabilities, resulting in data exposure, theft, or operational disruption.
What Causes Enterprise Data Breaches?
The most common causes of enterprise data breaches include:
- Weak identity and access management (IAM)
- Unpatched systems and outdated software
- Lack of continuous monitoring and detection
- Insecure endpoints and remote access exposure
- Poor incident response readiness
In fact, industry reports show that over 60% of breaches are caused by preventable security misconfigurations, not advanced attacks.
Key Benefits of Preventing Enterprise Data Breaches
- Avoid millions in financial losses, including recovery, downtime, and regulatory fines that can escalate beyond initial breach impact
- Protect long-term customer trust, because over 60% of customers permanently disengage after a breach
- Maintain compliance with GDPR, HIPAA, and global frameworks, avoiding penalties that scale with every exposed record
- Ensure uninterrupted operations by preventing system downtime that can last days or even weeks
- Strengthen cybersecurity maturity, transforming security from a reactive cost center into a strategic business advantage
However, most enterprises still fail to achieve these outcomes due to critical security gaps below.
Why Enterprise Data Breaches Are So Costly Today
Enterprise data breaches extend far beyond IT, they impact revenue, operations, compliance, and reputation simultaneously. The global average breach cost is now $4.45 million, while large enterprises in regulated industries often experience significantly higher losses.
1. Direct Financial Losses Can Exceed Millions
Organizations face immediate costs including forensic investigations, legal fees, regulatory fines, and system recovery. GDPR penalties alone can reach €20 million or 4% of global annual revenue, whichever is higher.
Impact: Even a single breach can destabilize enterprise financial performance.
2. Reputational Damage Reduces Revenue for Years
Over 60% of customers lose trust permanently after a data breach, resulting in long-term churn and reduced customer lifetime value.
Impact: Revenue loss continues long after the technical issue is resolved.
3. Compliance Violations Increase Legal Exposure
Regulations like GDPR, HIPAA, and CCPA impose strict penalties and audits. Non-compliance increases both financial and legal risk.
4. Operational Downtime Disrupts Business Continuity
Enterprise breaches can cause downtime lasting several days to weeks, directly affecting productivity, sales, and service delivery.
5. Hidden Costs Multiply Over Time
Hidden costs include cybersecurity upgrades, insurance hikes, customer compensation, and long-term reputation rebuilding.
Final insight: The true cost is not the breach itself, it is the long-term business damage it creates.
Top 5 Costly Mistakes That Lead to Enterprise Data Breaches
1. Weak Identity and Access Management (IAM)
Weak identity and access management is one of the most critical vulnerabilities in enterprise environments. In many cases, organizations fail to enforce strict authentication controls, leaving systems exposed to unauthorized access.
Why This Happens
Employees often use weak or reused passwords. Additionally, many enterprises do not implement multi-factor authentication (MFA), making it easier for attackers to compromise accounts.
Impact on Enterprise Data Breaches
Once access is gained, attackers can move laterally within the system. As a result, sensitive data becomes accessible, leading to major enterprise data breaches.
Prevention Strategy
Organizations must enforce strong authentication policies and adopt least-privilege access controls, supported by Cyberix Governance, Risk, and Compliance (GRC) to ensure consistent identity security and governance across the enterprise.
2. Unpatched Systems and Outdated Software
Unpatched systems remain one of the easiest entry points for attackers. However, many organizations delay updates due to operational concerns.
Why This Happens
Enterprises often prioritize uptime over security updates. Moreover, legacy systems make patching more complex.
Impact on Enterprise Data Breaches
Attackers exploit known vulnerabilities quickly. Consequently, outdated systems become direct gateways for enterprise data breaches.
H4: Prevention Strategy
Organizations should implement automated patch management and continuous vulnerability scanning through Cyberix Vulnerability Management to proactively identify, prioritize, and remediate security gaps before they can be exploited.
3. Poor Monitoring and Delayed Threat Detection
Without real-time monitoring, organizations lack visibility into ongoing threats. As a result, attackers can remain undetected for long periods.
Why This Happens
Many enterprises rely on fragmented security tools without centralized monitoring. Additionally, alert fatigue can cause teams to ignore critical warnings.
Impact on Enterprise Data Breaches
Delayed detection allows attackers to extract data over time. Therefore, breaches become more severe and costly.
Prevention Strategy
Organizations should adopt continuous monitoring and centralized threat detection powered by Cyberix Virtual Security Operations Center (vSOC) and Threat Detection to ensure real-time visibility, faster alerting, and immediate response to suspicious activity across the enterprise.
4. Weak Endpoint Security and Remote Access Exposure
The rise of remote work has increased reliance on endpoints, creating new vulnerabilities. Consequently, unsecured devices become easy entry points.
Why This Happens
BYOD policies and unsecured networks introduce risks. Moreover, endpoint security is often inconsistent across organizations.
Impact on Enterprise Data Breaches
Attackers exploit weak endpoints to access internal systems. As a result, organizations face large-scale enterprise data breaches.
Prevention Strategy
Organizations must strengthen endpoint protection and continuously monitor all connected devices through Cyberix Active Defense and Threat Hunting, enabling proactive identification and neutralization of threats before they can infiltrate enterprise systems.
5. Lack of Incident Response Planning
Even strong security systems can fail. However, the absence of a response plan significantly increases damage.
Why This Happens
Organizations often lack structured response frameworks and trained teams.
Impact on Enterprise Data Breaches
Delayed response leads to prolonged attacks and greater data loss. Therefore, the overall impact becomes much more severe.
Prevention Strategy
Organizations must develop and regularly test incident response plans with Cyberix Incident Response to ensure rapid containment, minimized damage, and faster recovery in the event of a security breach.
Key Components of a Strong Enterprise Cybersecurity Strategy
A strong cybersecurity strategy is essential to prevent enterprise data breaches, especially as attack surfaces continue to expand across cloud, endpoints, and third-party systems. In fact, organizations with mature security strategies can reduce breach costs by up to 30–40%, according to industry reports.
However, effective cybersecurity is not built on a single tool or solution. Instead, it requires a layered, integrated approach that combines visibility, intelligence, governance, and proactive defense.
1. Continuous Monitoring for Real-Time Visibility
Firstly, continuous monitoring is the foundation of enterprise security. Without real-time visibility, organizations cannot detect or respond to threats effectively.
Modern attackers can infiltrate systems and remain undetected for an average of 200+ days. As a result, organizations without monitoring capabilities face significantly higher breach impact.
Therefore, enterprises must implement centralized monitoring systems that provide real-time alerts and actionable insights.
2. Threat Intelligence to Stay Ahead of Attacks
In addition, threat intelligence enables organizations to anticipate and prevent attacks before they occur. Instead of reacting to incidents, enterprises can identify patterns, vulnerabilities, and emerging threats proactively.
Moreover, integrating threat intelligence reduces response time and improves decision-making during security incidents. Consequently, organizations can minimize exposure to enterprise data breaches.
3. Governance, Risk, and Compliance (GRC) Alignment
Moreover, governance frameworks ensure that security policies are consistently enforced across the organization. Without proper governance, even strong technical controls can fail.
Regulatory requirements such as GDPR and HIPAA demand strict compliance. Therefore, aligning cybersecurity strategy with governance reduces legal risks and strengthens accountability.
4. Layered Security Architecture (Defense-in-Depth)
Furthermore, relying on a single security layer is no longer sufficient. Modern cybersecurity requires a defense-in-depth approach, where multiple layers work together to protect systems.
This includes identity security, endpoint protection, network defense, and cloud security. As a result, even if one layer is compromised, others can prevent a full-scale breach.
5. Proactive Defense and Threat Hunting
Finally, proactive defense strategies allow organizations to identify threats before they escalate. Instead of waiting for alerts, security teams actively search for suspicious activity within systems.
Organizations using proactive threat hunting can reduce breach detection time by up to 50%. Therefore, this approach significantly lowers the risk and impact of enterprise data breaches.
Quick Strategy Checklist
Enterprises can use this checklist to quickly evaluate whether their cybersecurity strategy is strong enough to prevent enterprise data breaches. If an organization fails even 2–3 items below, it is already operating in a high-risk enterprise data breach exposure zone.
Core Security Controls
- Multi-factor authentication (MFA) is enforced across all critical systems
- Least-privilege access model is implemented for all users
- Regular patching cycle is automated and consistently applied
Monitoring and Detection
- 24/7 continuous monitoring is active across all endpoints and networks
- Centralized security dashboard provides real-time visibility
- Threat detection alerts are actively reviewed and acted upon
Governance and Compliance
- Security policies are aligned with GDPR, HIPAA, or relevant frameworks
- Regular internal and external security audits are conducted
- Risk management framework is actively maintained and updated
Incident Response Readiness
- A documented incident response plan is in place
- Response teams are trained and regularly tested through simulations
- Recovery and business continuity plans are clearly defined
Proactive Defense Capability
- Threat intelligence feeds are integrated into security systems
- Vulnerability scanning is performed continuously
- Active threat hunting is part of security operations
How Cyberix Helps Prevent Enterprise Data Breaches
Cyberix is not just a cybersecurity provider, it is a fully integrated enterprise security ecosystem designed to prevent, detect, and neutralize enterprise data breaches across every layer of your digital environment. Instead of relying on fragmented tools, Cyberix unifies intelligence, monitoring, defense, and compliance into one coordinated security framework.
Firstly, Cyberix delivers continuous visibility through a Virtual Security Operations Center (vSOC), ensuring that every system, endpoint, and cloud environment is monitored in real time. This enables organizations to detect anomalies instantly and respond before threats escalate into full-scale breaches.
Moreover, Cyberix strengthens proactive security through advanced Threat Hunting and Active Defense capabilities. Rather than waiting for alerts, security teams actively identify hidden threats and neutralize them before they impact business operations.
In addition, Cyberix significantly reduces risk exposure through comprehensive Vulnerability Management, Web Application Security Testing, and Cloud Security solutions. These services ensure that attack surfaces are continuously assessed, hardened, and secured against evolving threats.
Furthermore, in the event of an attack, Cyberix’s Incident Response and Recovery and Digital Forensics capabilities ensure rapid containment, root-cause analysis, and system restoration. This minimizes downtime, reduces financial impact, and preserves business continuity.
Finally, Cyberix extends protection across endpoints and data layers through Endpoint Security Management, Data Loss Prevention (DLP), and Breach Detection, ensuring that sensitive information is protected at every stage of its lifecycle.
Ultimately, Cyberix transforms cybersecurity from a reactive cost center into a proactive enterprise defense system, giving organizations full visibility, faster response, and stronger resilience against modern cyber threats.
Summary
Enterprise data breaches have become one of the most critical cybersecurity challenges for modern organizations, especially as businesses expand across cloud environments, remote work setups, and third-party systems. This blog explored the top 5 costly mistakes that lead to enterprise data breaches, including weak identity and access management, unpatched systems, poor monitoring, insecure endpoints, and lack of incident response planning. Each of these mistakes creates security gaps that attackers can easily exploit, often leading to financial loss, operational disruption, and reputational damage.
To address these risks, enterprises must adopt a proactive, layered cybersecurity strategy that combines continuous monitoring, threat intelligence, governance frameworks, and rapid response capabilities. With solutions like Cyberix Virtual SOC, Threat Hunting, Vulnerability Management, GRC, and Incident Response, organizations can detect threats early, reduce exposure, and respond effectively. Ultimately, preventing enterprise data breaches is not just an IT priority, it is a business-critical requirement for long-term resilience and growth.
Conclusion
Enterprise data breaches are rarely random events, they are the direct result of overlooked, repeated, and entirely preventable security gaps. However, organizations that proactively identify and eliminate these weaknesses can significantly reduce both risk exposure and financial impact.
Therefore, enterprises must prioritize strong access control, continuous monitoring, and well-structured incident response planning as core pillars of their cybersecurity strategy. These are not optional improvements, they are essential safeguards for modern digital operations.
Moreover, adopting a proactive, layered cybersecurity approach ensures long-term resilience against evolving threats. Instead of reacting after damage occurs, organizations can shift toward prevention, early detection, and rapid containment, dramatically reducing the likelihood and severity of enterprise data breaches.
Ultimately, cybersecurity maturity is no longer just an IT objective, it is a business survival requirement in today’s threat landscape.
Take the Next Step with Cyberix
If your organization wants to eliminate the risks of enterprise data breaches, now is the time to act. Book a consultation with Cyberix and build a breach-resistant enterprise today.
FAQs
-
What is an enterprise data breach?
An enterprise data breach is a cybersecurity incident where unauthorized users gain access to sensitive business data such as customer records, financial information, or internal systems. These breaches usually occur due to weak security controls, vulnerabilities, or misconfigurations.
-
What are the main causes of enterprise data breaches?
The most common causes include weak identity and access management, unpatched software, lack of monitoring, insecure endpoints, and poor incident response planning. These issues allow attackers to access and exploit enterprise systems.
-
How much does an enterprise data breach cost?
On average, an enterprise data breach costs around $4.45 million globally, according to industry reports. However, the total cost can be much higher depending on regulatory fines, downtime, and reputational damage.
-
Why are enterprise data breaches so damaging?
They are damaging because they impact multiple areas at once, financial loss, customer trust, regulatory compliance, and operational continuity. In many cases, businesses lose customers and revenue long after the breach is resolved.
-
How can enterprises prevent data breaches?
Enterprises can prevent data breaches by implementing multi-factor authentication, continuous monitoring, vulnerability management, threat intelligence, and a strong incident response plan. A layered cybersecurity strategy is essential.
-
What is the role of Cyberix in preventing enterprise data breaches?
Cyberix provides an integrated cybersecurity ecosystem that includes vSOC, threat hunting, active defense, incident response, GRC, vulnerability management, and breach detection. It helps organizations detect and prevent threats in real time.
-
What is the biggest mistake companies make in cybersecurity?
One of the biggest mistakes is weak identity and access management, where employees use weak passwords or excessive permissions are granted. This allows attackers to gain unauthorized access to critical systems.