Introduction: Virtual SOC Is Now a Critical Security Layer in 2026
Virtual SOC has become a core cybersecurity requirement in 2026 as organizations face nonstop, automated cyberattacks across cloud, hybrid, and remote environments.
A Virtual Security Operations Center delivers 24/7 monitoring, threat detection, and incident response without requiring an internal SOC team. Instead, it centralizes security operations through a managed model that combines automation, threat intelligence, and cybersecurity experts.
As digital infrastructure expands across SaaS platforms, cloud systems, and distributed networks, traditional security setups struggle to maintain real-time visibility and rapid response.
This gap is pushing businesses toward Virtual SOC services to improve detection speed, reduce operational overhead, and strengthen overall security posture.
In this blog, you will understand what a Virtual SOC is, how it works, why it matters in 2026, and how Cyberix helps organizations build continuous cyber resilience.
What Is a Virtual SOC (vSOC)
A Virtual SOC (Virtual Security Operations Center) is a cloud-based cybersecurity model that delivers 24/7 threat monitoring, detection, investigation, and response without requiring an organization to operate an in-house security operations center.
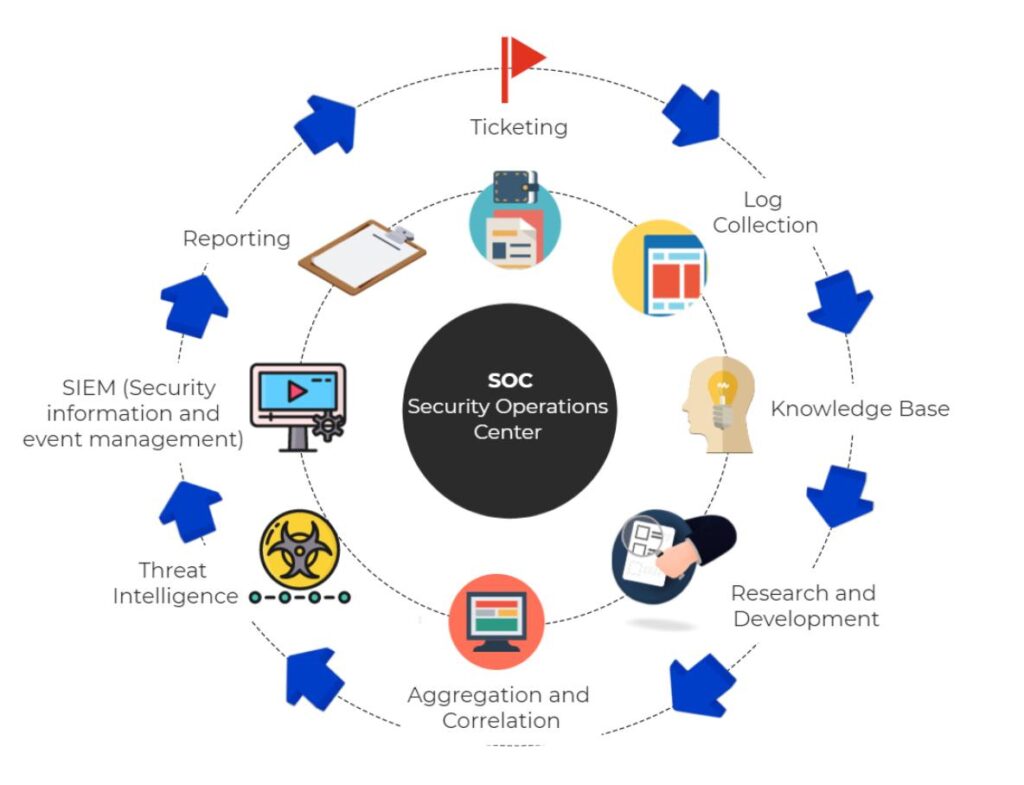
It functions as a centralized security layer where security tools, automation systems, threat intelligence, and cybersecurity experts work together to monitor digital environments in real time.
Instead of managing infrastructure, hiring SOC teams, and maintaining complex tooling internally, organizations use a Virtual SOC to gain continuous visibility across cloud systems, endpoints, applications, and networks.
This model is delivered through SOC as a Service, making enterprise-grade cybersecurity more scalable and operationally efficient.
In simple terms, a Virtual SOC ensures that threats are detected early, analyzed quickly, and responded to before they can cause business disruption.
Why Businesses Need a Virtual SOC in 2026
Cyber Threats Are Now Continuous and Automated
Cyberattacks in 2026 are no longer isolated events. Instead, they run continuously using automated tools that scan, exploit, and move across systems in real time. Because of this, businesses without constant monitoring often detect threats only after damage has already occurred.
A Virtual SOC solves this by providing 24/7 visibility across all digital environments. It ensures that suspicious activity is identified and escalated immediately, reducing the time attackers have inside systems.
Security Teams Cannot Keep Up with Modern Attack Volume
The number of alerts, logs, and security events generated daily has grown beyond what most internal teams can handle effectively. This leads to delayed responses, missed threats, and operational overload.
A Virtual SOC centralizes this workload through automation and expert analysis. It filters noise, prioritizes real threats, and ensures that security teams focus only on high-risk incidents that require action.
The Cybersecurity Talent Gap Is Increasing
Hiring and retaining skilled cybersecurity professionals has become one of the biggest challenges for organizations. SOC analysts, threat hunters, and incident responders are in short supply, making it difficult to maintain a fully staffed internal SOC.
A Virtual SOC removes this dependency by providing immediate access to a complete team of security experts without recruitment delays or training overhead.
Real-Time Visibility Is Now a Business Requirement
Modern businesses operate across cloud platforms, remote systems, and third-party integrations. This distributed environment creates blind spots that attackers can exploit.
A Virtual SOC ensures continuous monitoring across all assets, giving organizations real-time visibility and faster response capability regardless of location or infrastructure complexity.
Virtual SOC vs Traditional SOC
Operational Model Difference
A traditional SOC is built and managed internally, meaning the organization is responsible for infrastructure, staffing, tooling, and 24/7 operations. This creates a heavy operational burden that grows with scale.
A Virtual SOC, on the other hand, is delivered as a managed service. Security operations are handled externally through a centralized system that combines tools, automation, and cybersecurity experts. This removes the need for internal SOC setup while maintaining full security coverage.
Cost and Resource Efficiency
Traditional SOCs require high upfront investment in security tools, infrastructure, and skilled personnel. Ongoing costs like salaries, training, and system maintenance further increase total ownership cost.
A Virtual SOC replaces this with a predictable service-based model. Organizations pay for continuous protection without managing infrastructure or building large internal teams, making it significantly more cost-efficient.
Detection Speed and Response Time
In a traditional SOC, detection and response depend heavily on internal staffing levels and shift coverage, which can lead to delays during off-hours or high alert volumes.
A Virtual SOC operates continuously with automated detection and distributed security teams, enabling faster identification, escalation, and response to threats in real time.
Scalability and Flexibility
Scaling a traditional SOC requires additional hiring, infrastructure expansion, and tool integration, which slows down adaptability.
A Virtual SOC scales instantly with business growth. It adapts to new systems, cloud environments, and increased data flow without requiring internal restructuring or additional operational complexity.
Key Benefits of a Virtual SOC
A Virtual SOC helps organizations strengthen cybersecurity posture while reducing operational burden and improving response speed. It replaces complex in-house security setups with a scalable, always-on managed security model.
Key benefits include:
- 24/7 continuous monitoring across cloud, endpoints, applications, and networks for real-time threat visibility
- Faster threat detection and response using automation, SIEM, and expert-led analysis
- Lower operational and infrastructure costs by eliminating the need for an in-house SOC setup
- Immediate access to cybersecurity experts including analysts, incident responders, and threat hunters
- Reduced risk exposure through early detection and rapid containment of security incidents
- Scalable security operations that adapt easily to business growth and cloud expansion
- Improved compliance readiness with structured reporting and governance alignment
What Services Are Included in a Virtual SOC
A Virtual SOC is a complete cybersecurity ecosystem that combines monitoring, detection, response, and prevention into a single managed framework. It goes beyond simple alerting by delivering end-to-end protection across all digital environments.
Core services typically include:
- 24/7 Security Monitoring (vSOC Operations)
Continuous monitoring of networks, endpoints, cloud platforms, and applications for real-time threat detection - Incident Response and Recovery
Rapid containment, investigation, and recovery from security incidents to minimize business impact - Threat Hunting
Proactive search for hidden or advanced threats that bypass automated detection systems - Breach Detection and Analysis
Identification of unauthorized access, abnormal behavior, and potential data exfiltration attempts - Active Defense Capabilities
Dynamic response mechanisms that adapt security controls based on evolving threat activity - Penetration Testing
Simulated attacks to identify vulnerabilities before attackers can exploit them - Vulnerability Management
Continuous scanning and prioritization of security weaknesses for timely remediation - Cloud Security Monitoring
Protection of cloud infrastructure from misconfigurations, unauthorized access, and exposure risks - Data Loss Prevention (DLP)
Controls to prevent unauthorized movement or leakage of sensitive data - Endpoint Security Management
Protection of devices such as laptops, servers, and mobile endpoints from malware and intrusion - Security Awareness and Phishing Simulation
Employee-focused training and testing to reduce human-based security risks - Governance, Risk, and Compliance (GRC)
Alignment with regulatory frameworks, audit readiness, and structured risk management - Digital Forensics
Deep investigation of security incidents to trace attack origin, impact, and methods
Challenges of Building an In-House SOC
Building an in-house Security Operations Center is far more complex than it appears on paper. While it may seem like a strong security investment, the reality is that it requires continuous funding, specialized talent, and 24/7 operational discipline that most organizations struggle to sustain.
High Cost and Scalability Pressure
One of the most critical challenges is cost scalability. An internal SOC demands continuous investment in infrastructure, tools, and skilled personnel.
Key cost drivers include:
- SIEM platforms and log management systems
- Threat intelligence subscriptions
- Endpoint and network monitoring tools
- Salaries for specialized cybersecurity staff
As the organization grows, these costs increase continuously, making long-term scalability difficult and financially inefficient.
Cybersecurity Talent Shortage
Another major constraint is the global shortage of cybersecurity professionals. Skilled SOC analysts and incident responders are difficult to hire and even harder to retain.
Common talent-related challenges include:
- Limited availability of experienced security analysts
- High recruitment and retention costs
- Burnout due to high-pressure monitoring roles
- Skill gaps in advanced threat handling
Even when teams are built successfully, maintaining consistent expertise across all shifts becomes a challenge.
Operational Complexity and Tool Overload
Modern SOC environments rely on multiple security tools working together in real time. Without tight integration, operations become fragmented and inefficient.
This leads to:
- Multiple disconnected security dashboards
- Delayed threat correlation across systems
- Manual effort in investigating alerts
- Reduced visibility across hybrid environments
As complexity increases, operational efficiency often decreases instead of improving.
24/7 Monitoring Challenges
Cybersecurity is not limited to business hours, which makes continuous monitoring essential. However, maintaining true 24/7 coverage internally is extremely resource-intensive.
Typical issues include:
- Limited staffing for night and weekend shifts
- Gaps in monitoring during off-hours
- Slower response times during low coverage periods
- Higher risk of undetected breaches
Even short delays in detection can be exploited by attackers, making this one of the most critical vulnerabilities in in-house SOC models.
Key Reality Check
In practice, most organizations eventually realize that an in-house SOC requires enterprise-level resources, continuous staffing, and constant operational maturity just to maintain baseline security coverage.
Why Cyberix for Virtual SOC
Cyberix delivers a Virtual SOC (vSOC) built for continuous protection, real-time visibility, and enterprise-grade threat response without the complexity of managing an in-house security operations center.
Unlike traditional security setups that rely on fragmented tools and internal teams, Cyberix centralizes cybersecurity operations into a unified managed framework. This ensures that threats are not only detected but actively investigated and neutralized before they escalate.
Cyberix combines 24/7 security monitoring, AI-driven threat detection, and expert-led incident response to maintain constant defense across cloud environments, endpoints, applications, and networks. This reduces response time and significantly improves threat containment efficiency.
The platform also integrates proactive capabilities such as Threat Hunting, Breach Detection, and Active Defense, ensuring that hidden and advanced threats are identified before causing damage.
In addition, Cyberix strengthens overall security posture through services like Penetration Testing, Vulnerability Management, Cloud Security, Data Loss Prevention, and Governance, Risk, and Compliance (GRC). This creates a complete security ecosystem rather than isolated point solutions.
What makes Cyberix different is its ability to scale with business growth while maintaining consistent security performance. Whether an organization is expanding cloud infrastructure or increasing digital operations, the Virtual SOC adapts without requiring internal restructuring or added operational burden.
Key Takeaways
- A Virtual SOC is a critical cybersecurity requirement in 2026 due to continuous, automated, and highly advanced cyber threats targeting cloud, hybrid, and remote environments.
- It provides 24/7 monitoring, threat detection, and incident response without the need for building and maintaining an in-house Security Operations Center.
- A Virtual SOC combines automation, SIEM platforms, threat intelligence, and cybersecurity experts to deliver real-time visibility and faster threat response.
- Compared to traditional SOCs, it is more scalable, cost-efficient, and operationally flexible, removing the burden of infrastructure, staffing, and tool management.
- It helps organizations overcome major challenges such as talent shortages, alert overload, and limited 24/7 coverage.
- Businesses gain enterprise-grade security without internal complexity, making advanced cybersecurity accessible even for mid-sized organizations.
- It ensures faster detection and reduced dwell time, significantly lowering the impact of cyber incidents.
- A Virtual SOC supports compliance, risk management, and governance requirements through structured monitoring and reporting.
- It enables a shift from reactive security to proactive, intelligence-driven defense strategies.
- Ultimately, it strengthens overall cyber resilience while allowing businesses to focus on growth instead of security operations overhead.
Conclusion
Cyber threats in 2026 are faster, more automated, and more persistent than ever. Without continuous monitoring and rapid response, organizations remain exposed to risks that can disrupt operations and compromise sensitive data.
A Virtual SOC powered by Cyberix helps businesses move from reactive security to a proactive, intelligence-driven defense model with 24/7 protection and real-time threat response.
If your organization is ready to strengthen its cybersecurity posture and eliminate visibility gaps, now is the time to act.
Connect with Cyberix to deploy a Virtual SOC built for continuous monitoring, faster incident response, and scalable enterprise security.
Frequently Asked Questions (FAQs)
Virtual SOC is a cloud-based cybersecurity model that provides continuous monitoring, threat detection, and incident response without requiring an in-house security operations center.
What is a Virtual SOC in simple terms?
A Virtual SOC is a managed security service that monitors an organization’s systems 24/7 to detect and respond to cyber threats in real time.
How is a Virtual SOC different from a traditional SOC?
A traditional SOC is built and managed internally, requiring high costs and dedicated teams. A Virtual SOC is outsourced, scalable, and provides continuous monitoring without internal infrastructure.
Is a Virtual SOC suitable for small and mid-sized businesses?
Yes. A Virtual SOC is especially beneficial for organizations that need enterprise-grade security but cannot afford or manage a full in-house SOC.
Does a Virtual SOC work with cloud environments?
Yes. A Virtual SOC is designed to secure cloud, hybrid, and on-premise environments with full visibility and real-time monitoring.
How quickly can a Virtual SOC respond to threats?
Response time is significantly faster because it combines automation, SIEM tools, and expert analysts working together in real time.